
Protecting Critical Data from Phishing and Other Insider Threats
January 21, 2021
Password Best Practices
May 12, 20225 Significant Risks IoT Devices Pose for Data & Privacy
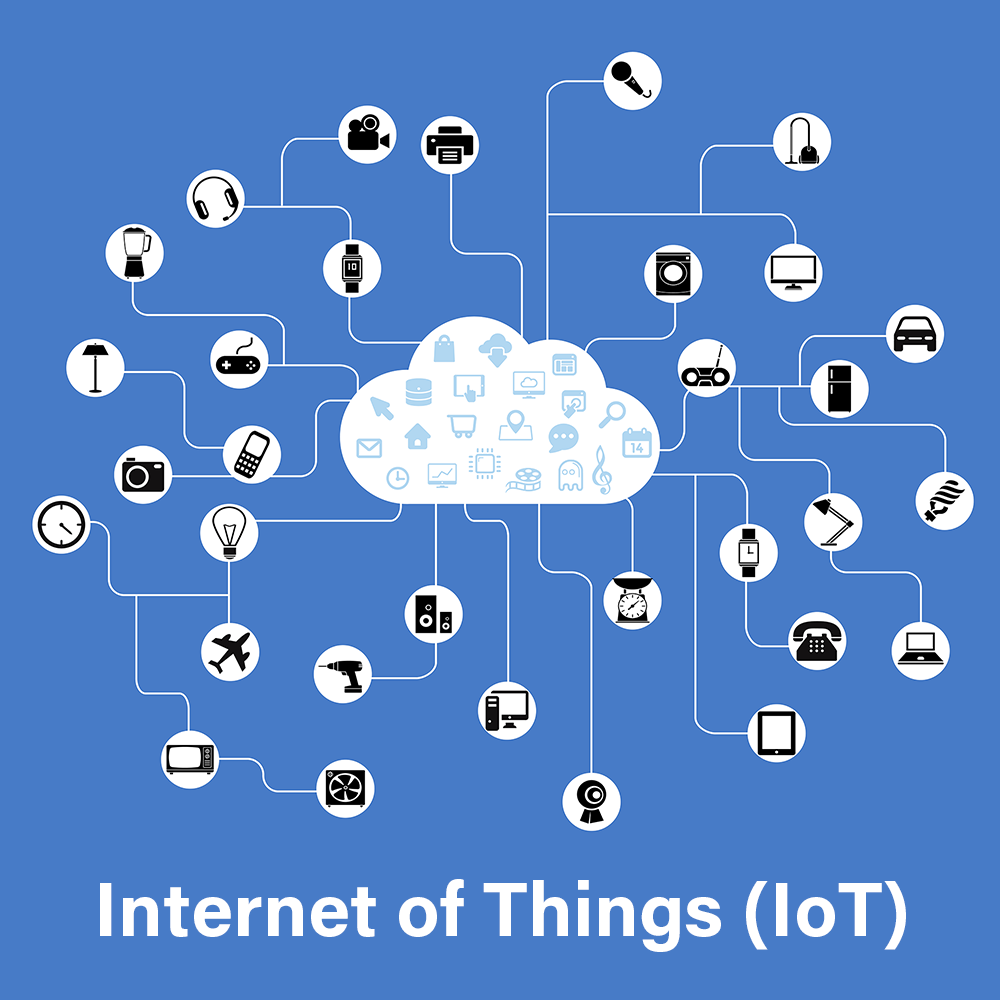 Gartner projected that by 2023, CIOs will be responsible for more than triple the number of endpoints they were accountable for in 2018 due to the rapid evolution of Internet of Things (IoT) technologies. With billions of physical devices worldwide connected to the internet, this prediction seems to be becoming a reality. However, the advancement of IoT technology has proved to be a double-edged sword when it comes to cybersecurity and compliance.
Gartner projected that by 2023, CIOs will be responsible for more than triple the number of endpoints they were accountable for in 2018 due to the rapid evolution of Internet of Things (IoT) technologies. With billions of physical devices worldwide connected to the internet, this prediction seems to be becoming a reality. However, the advancement of IoT technology has proved to be a double-edged sword when it comes to cybersecurity and compliance.
IoT devices generate massive volumes of various data types that are stored, managed, and shared within an organization's IT infrastructure. Consequently, they add to the risk landscape concerning cybersecurity, third-party risk, and compliance with data protection regulations.
Securing IoT devices is not only about safeguarding the device itself but also securing the access they provide. Apart from examining the device's inherent vulnerabilities, one must also consider how and where IoT devices connect to the network, how they handle and store data, and their user interface.
Throughout this article, we'll explore how IoT devices can be exploited, the top 5 threats they pose to data protection and privacy, and why it's essential to secure them from a compliance standpoint. It's vital to pay close attention to protecting your organization from security disasters and avoid penalties and lawsuits that may result from non-compliance with current regulations.
Internet of Things (IoT) Applications & Device Examples
Here is a brief list of common, real-world applications with associated popular device examples.
- Wearables - Any connected device on (or in) a person’s body, like a smartwatch (Apple Watch or Fitbit, etc.) and medical devices like implanted pacemakers, glucose monitors, etc.
- Smart Homes - Smart speakers (as they are sometimes called), like Apple HomePod, Amazon Echo, Google Home, Nest, etc., can more accurately be described as smart microphones.
- Connected Cars and Trucks - Connected vehicles use internet connectivity to communicate with outside systems, including but not limited to apps that can unlock your car, smart maps, emergency response systems, and vehicle-to-vehicle communications.
- Smart Cities - Some cities, especially in Europe and Asia are quite connected, using devices to help reduce issues like traffic congestion, noise/air pollution, and crime, to name a few.
How IoT Devices Can Be Exploited
IoT devices are primarily compromised through these attack vectors:
- The Devices - Cybercriminals commonly take advantage of vulnerabilities in the memory, firmware, physical interface, web interface, and network services of IoT devices. Moreover, other factors, such as unsecured default settings, outdated components, and unsecured update mechanisms, can also be exploited.
- Communication Channels - Attacking the communication channel that connects an IoT device to other devices can also result in its compromise. The use of insecure protocols in IoT systems can create security vulnerabilities that could jeopardize the entire network, making it vulnerable to network attacks such as denial of service (DoS) and spoofing.
- Applications and Software - Cybercriminals with malicious intent can take advantage of vulnerabilities in web applications and associated software for IoT devices. For example, this could involve targeting web applications to steal user credentials or distribute malware.
Significant Threats to IoT Security
Now that we understand how IoT devices can be used maliciously and harm your business, let's examine the five significant threats these devices present to data protection and privacy. Failing to take the appropriate steps to address these threats and maintain documentation of your efforts could lead to penalties for non-compliance with at least one data protection regulation in the future.
Extensive and Improper Data Collection
IoT sensors and devices gather vast quantities of precise information regarding their surroundings and users, sometimes without explicit consent or knowledge, including sensitive data. Consequently, depending on your business or industry's regulatory requirements, this information must be protected in the same manner as other sensitive data within your network. For instance, if you acquire medical data in the United States through a group of IoT devices, you must protect it in accordance with HIPAA regulations.
Provides Backdoor Access for Cybercriminals
Just one inadequately secured IoT device is all that a cybercriminal needs to launch a devastating attack on your network. Moreover, an unscrupulous insider could also leverage an unsecured IoT device to execute a comprehensive cyber assault on your organization. Ignoring these potential threats is unacceptable according to any data protection regulation, and thus demands prompt action.
- About 60% of IoT devices are vulnerable to medium- or high-severity attacks - 2020 Unit 42 IoT Threat Report
- Over 95% of all IoT device traffic is unencrypted - 2020 Unit 42 IoT Threat Report
- About 72% of organizations experienced increased endpoint and IoT security incidents last year and 56% of organizations expect to be compromised via endpoint or IoT-related attacks within the next 12 months - 2020 Endpoint and IoT Zero Trust Security Report
A Solitary Security Policy is Insufficient
IoT environments are intricate and contribute to the intricacy of your IT system. Due to their distinctive characteristics, it is neither practical nor presently feasible to establish a universal security policy that applies to all IoT devices. The exponential increase in remote work has only magnified this challenge. For instance, even though many businesses may not have employees' personal devices in the office during the COVID-19 pandemic, employees may have access to them in their homes (which now function as their offices), allowing business-related work and data to be jeopardized by exploiting such devices.
As per Ponemon Institute's 2021 Data Exposure Report, home networks are 71 percent less secure than office networks. If your organization neglects to address this hazard, it may lead to dire consequences when compliance auditors investigate.
Lack of Comprehensive IoT Security Awareness Training
Security awareness training is a strong approach to minimizing the possibility and severity of cyberattacks. Nonetheless, the absence of widespread knowledge and awareness at the user level regarding IoT poses a formidable risk to the security of IoT data. It is an enormous task to educate all personnel on IoT functionality and the associated risks. Compliance regulations worldwide regard security awareness training as a critical component of the data protection framework. The absence of this training could lead to unfavorable results during a compliance audit for your business or organization.
Privacy Threats
Undoubtedly, IoT devices pose a direct danger to the privacy of yourself and your customers. Every piece of information they disclose about your organization via an IoT device represents a portion of privacy surrendered. Hence, it is our duty to safeguard client privacy and data. Failing to do so could result in significant consequences. For instance, according to the EU's GDPR, each user must have the "right to be forgotten," and if your business is unable to fulfill this requirement, non-compliance penalties will apply.
IoT Risks and Loose Compliance
Even though there may be no globally recognized regulatory prerequisites or "standards" for IoT device security, it is unwise to assume that worldwide regulators are unconcerned with the dangers posed to IoT devices and data. This is not only a cybersecurity issue but also a compliance matter. Investing in appropriate security solutions will improve your organization's cybersecurity position against IoT-associated risks. Nevertheless, to overcome this challenge from a compliance perspective, you undoubtedly could use additional support.
By utilizing Hixardt’s automated cybersecurity and compliance process platforms, we can assist you in identifying IoT risks during standard risk assessments, implementing corrective actions, and generating compliance documentation automatically. In addition, you can avoid IoT-associated risks associated with compliance standards such as HIPAA, GDPR, CMMC, NIST CSF, and your cyber insurance policy. Simply send sales@hixardt.com an email, and we will assist you in getting started.
This article is curated and used with the permission of the copyright holder.
- - -
About Hixardt Technologies
©2021 Hixardt Technologies, Inc. All rights reserved. Hixardt and the Hixardt logo are among the trademarks or registered trademarks owned by or licensed to Hixardt Technologies, Inc. All other marks are the property of their respective owners.
The advancement of IoT technology has proved to be a double-edged sword when it comes to cybersecurity and compliance.




